Our team often contributes to open-source, community, and other research projects.
Below are several examples of these contributions to the security community:
Projects
KillerBee 2.0
KillerBee software is intended for students, researchers, engineers, and security professionals to use for evaluating the security of IEEE 802.15.4/ZigBee systems. River Loop is a leader in IEEE 802.15.4 and ZigBee security research and penetration testing, and is proud to contribute to the open-source and security community through the continued development of KillerBee along with other contributors.
ApiMote IEEE 802.15.4/ZigBee Sniffing Hardware
The ApiMote v4beta version is beta hardware intended for students, researchers, engineers, and security professionals to use for learning about and evaluating the security of IEEE 802.15.4/ZigBee systems.
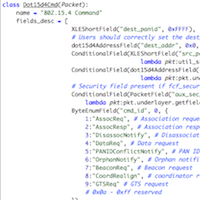
Scapy dot15d4
Scapy dot15d4 is a IEEE 802.15.4 dissection/construction layer for the popular Scapy packet manipulation framework. Others have joined in to extend this to make it a leading tool for evaluating the security of IEEE 802.15.4/ZigBee systems.
Conferences
DEF CON 26
River Loop had the privilege of presenting our latest efforts in wireless fuzzing, including the TumbleRF software framework and the Orthrus offensive radio interface, at DEF CON 26 in Las Vegas, NV. This research highlights the importance of securing oft-overlooked system components, such as non-IP network interfaces and hardware buses. 2014’s Isotope 802.15.4 bugs highlighted an interesting class of vulnerability existing at the PHY layer, so we wrote some tools to make uncovering bugs like those more systematic.
Black Hat 2018
River Loop was thrilled to present its TumbleRF fuzzing framework at Black Hat Arsenal, a forum dedicated to open source security research and software at Black Hat USA. TumbleRF is an open source Python framework that enables researchers to fuzz arbitrary RF technologies down to the PHY. As River Loop’s 2014 Isotope research demonstrated, PHY-layer bugs can have serious implications, and often hide in plain sight. Thus, developing a tool to make finding these bugs systematic seemed like a good fit.
Hardware Security Training Talks: IEEE 802.15.4 Overview and TumbleRF Fuzzing
In this talk, we shared with the assembled group of hardware security professionals and students an introduction to IEEE 802.15.4 security and showed a few basic attacks, an intermediate attack, and then two examples of advanced techniques and research.
Troopers 18: Unifying RF Fuzzing Techniques under a Common API: TumbleRF
While fuzzing is known to be a powerful mechanism for fingerprinting and enumerating bugs within hardware and software systems, the application of this technique to wireless systems remains nontrivial due to fragmented and siloed tools. In this talk, we covered wireless fuzzing fundamentals and introduce a new tool to unify the approach across protocols, radios, and drivers and released a new open-source tool to assist.
Troopers 14: Making (and Breaking) an IEEE 802.15.4 WIDS
Presented the ApiMote v4beta hardware for sniffing and injection on IEEE 802.15.4 networks and released as open source. Demonstrated the beta BeeKeeper WIDS framework for wireless intrusion detection on 802.15.4. Showed a technique for injecting packets which are seen at the PHY layer by some radio-chips but not by other chips, even when both chips are IEEE 802.15.4 compliant. You can download a copy of the presentation here.
ToorCon Seattle '11: Tools for Practical Exploration of the 802.15.4 Attack Surface
Presented toolkit for interacting with IEEE 802.15.4/Zigbee. Our tools build on top of the KillerBee framework developed by Josh Wright, and add support for additional hardware, code stability, as well as additional functionality such as reflexive jamming. In addition to a brief introduction to the issues of 802.15.4 security, demonstrated attendees how to get involved in attacking the surface themselves – the hardware and software they need – and showed how this enables them to not only perform their own assessments, but how it can provide attackers a way to interfere with the operation of networks as well.
ShmooCon '11: ZigBee Security: Find, Fix, Finish
Techniques for sniffing ZigBee packets have been presented, as have theoretical vulnerabilities in other types of wireless sensor networks, but this talk uses injection and intelligent packet generation to move towards real proof-of-concept attacks on 802.15.4/ZigBee networks.
We analyze which proposed wireless sensor network attacks actually work on ZigBee, and provide proof of concept implementations of theoretical attacks.
Publications
These are some of the published articles we have authored or co-authored:
PoC||GTFO: A Tourist’s Phrasebook for Reversing Embedded ARM in the Dialect of the Cortex M Series
This article in PoC||GTFO is a “quick-start” style guide for reversing engineering embedded systems. The goal is to get the reader situated with the ARM Cortex M architecture as quickly as possible, so they can apply their other reversing experience to this platform.
PoC||GTFO: A Tourist's Guide to MSP430
This article in PoC||GTFO is a “quick-start” style guide for reversing engineering embedded systems. The goal is to get the reader situated with the MSP430 architecture as quickly as possible, so they can apply their other reversing experience to this platform.
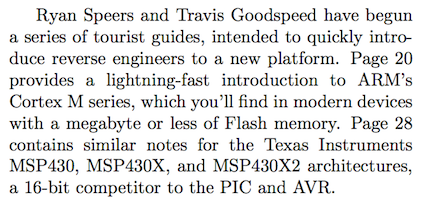
Workshop on Embedded Systems Security: Perimeter-Crossing Buses: a New Attack Surface for Embedded Systems
Any channel crossing the perimeter of a system provides an attack surface to the adversary. Standard network interfaces, such as TCP/IP stacks, constitute one such channel, and security researchers and exploit developers have invested much effort into exploring the attack surfaces and defenses there. However, channels such as USB have been overlooked, even though such code is at least as complexly layered as a network stack, and handles even more complex structures; drivers are notorious as a breeding ground of bugs copy-pasted from boilerplate sample code.
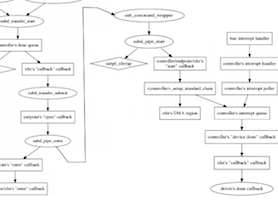
USENIX Workshop on Offensive Technologies: Packets in Packets: Orson Welles’ In-Band Signaling Attacks for Modern Radios
Presents methods for injecting raw frames at Layer 1 from within upper-layer protocols by abuse of in-band signaling mechanisms common to most digital radio protocols. This packet piggy-backing technique allows attackers to hide malicious packets inside packets that are permitted on the network.
Hawaii International Conference on System Sciences/IEEE Computer Society: Api-do: Tools for Exploring the Wireless Attack Surface in Smart Meters
Security is critical for the wireless interface offered by soon-to-be-ubiquitous smart meters; if not secure, this technology provides an remotely accessible attack surface distributed throughout many homes and businesses. History shows, however, that new network interfaces remained brittle and vulnerable (although believed otherwise) until security researchers could thoroughly explore their attack surface.