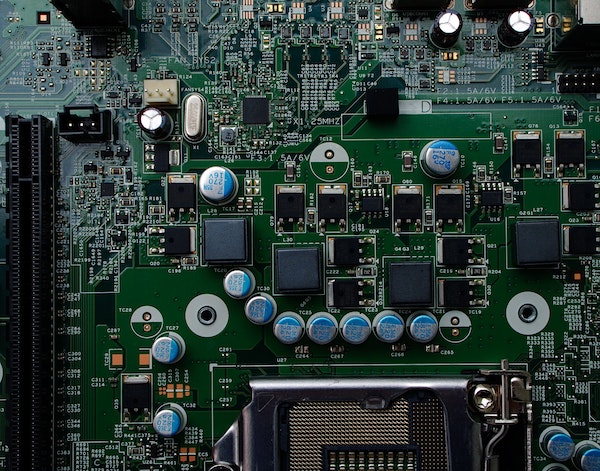
Small Scale Circuit Board Assembly: A Working Guide
Here at River Loop Security, we’re tightly focused on solving hardware security challenges. The nature of our work frequently brings us into contact with problems that: deal with intricate technical details of ICs, electrical systems, and products are, by their very nature, technically risky - we frequently run across challenges with no known solutions, and, as such, we have to try out technical approaches that can only be verified experimentally.