KillerBee 2.0
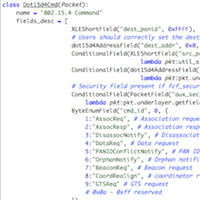
KillerBee software is intended for students, researchers, engineers, and security professionals to use for evaluating the security of IEEE 802.15.4/ZigBee systems. River Loop is a leader in IEEE 802.15.4 and ZigBee security research and penetration testing, and is proud to contribute to the open-source and security community through the continued development of KillerBee along with other contributors.