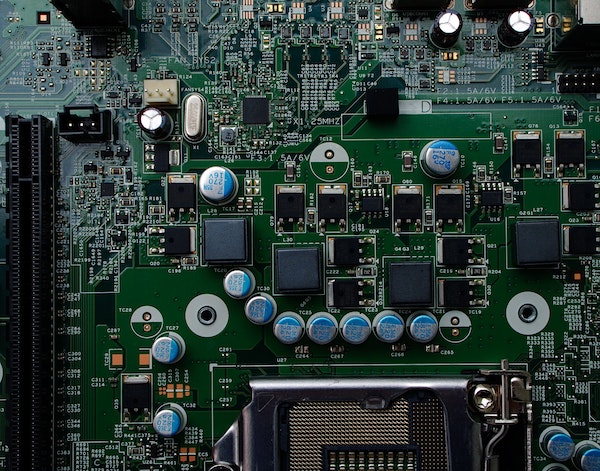
Small Scale Circuit Board Assembly: A Working Guide
Here at River Loop Security, we’re tightly focused on solving hardware security challenges. The nature of our work frequently brings us into contact with problems that:
- deal with intricate technical details of ICs, electrical systems, and products
- are, by their very nature, technically risky - we frequently run across challenges with no known solutions, and, as such, we have to try out technical approaches that can only be verified experimentally.
These two factors mean that we end up designing and fabricating a lot of circuit boards. It’s often the fastest way to quickly prove out hardware security techniques. We’ve come to find that traditional turnkey circuit board manufacturing is both too expensive and, crucially, too slow to meet our needs. Over the years, we’ve accumulated a lot of knowledge of how to quickly create circuit boards for testing hardware security proof of concepts. We wanted to share an explanation of our most basic low-quantity hand-assembly process in the hope that it helps others.